Buffer Overflow Attacks Pdf
In and, a buffer overflow, or buffer overrun, is an where a, while writing to a, overruns the buffer's boundary and overwrites adjacent locations. Buffers are areas of memory set aside to hold data, often while moving it from one section of a program to another, or between programs. Buffer overflows can often be triggered by malformed inputs; if one assumes all inputs will be smaller than a certain size and the buffer is created to be that size, then an anomalous transaction that produces more data could cause it to write past the end of the buffer. If this overwrites adjacent data or executable code, this may result in erratic program behavior, including memory access errors, incorrect results, and. Exploiting the behavior of a buffer overflow is a well-known. On many systems, the memory layout of a program, or the system as a whole, is well defined. Principles Of Construction Management By Roy Pilcher Wwe Tlc Match Game. here. By sending in data designed to cause a buffer overflow, it is possible to write into areas known to hold, and replace it with malicious code.
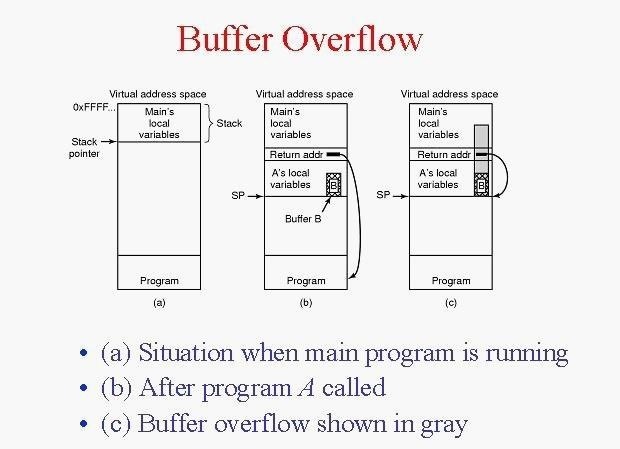
Buffers are widespread in (OS) code, so it is possible to make attacks that perform and gain unlimited access to the computer's resources. The famed in 1988 used this as one of its attack techniques. Commonly associated with buffer overflows include and, which provide no built-in protection against accessing or overwriting data in any part of memory and do not automatically check that data written to an (the built-in buffer type) is within the boundaries of that array.
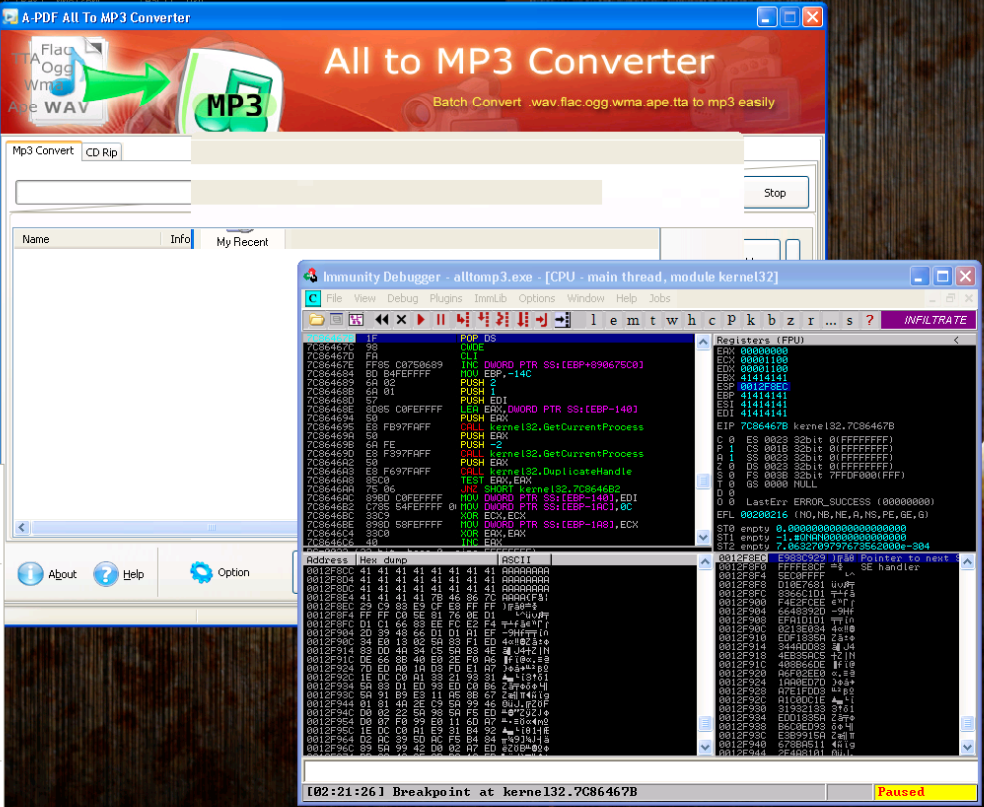
Jan 14, 2011 - Most prominent example: Buffer overflow. Sadeghi, Davi @TU Darmstadt 2010. Secure, Trusted and Trustworthy Computing, Part 1. Runtime Attacks. Figure: Buffer Overflows according to NIST Vulnerability Database. Sadeghi, Davi. Create a malicious PDF file containing (1) ROP code and (2). Apr 4, 2017 - Buffer Overflow Attack: Overrunning the. Memory Allocated on the Call Stack. Demonstration of Program Misbehavior. Caused by Buffer Overflow. Using gdb to Craft Program Inputs for. Exploiting Buffer-Overflow Vulnerability. Using Buffer Overflow to Spawn a Shell. Stack based buffer overflow Exploitation-Tutorial By Saif El -Sherei www.elsherei.com Thanks to: Haroon meer Sherif El Deeb http://www.eldeeb.net.
Comments are closed.